Data Encryption
Data encryption involves the conversion of plain, unencrypted data (plaintext) into coded, encrypted data (ciphertext) using an encryption algorithm and a specific encryption key. This process is employed to safeguard sensitive information and shield it from unauthorized access or interception, whether during transmission or storage. Encryption ensures that even if a malicious entity gains access to the encrypted data, they cannot comprehend or utilize it without the appropriate decryption key.
Key principles related to data encryption:
- Encryption Algorithm: An encryption algorithm is a mathematical formula, or a set of rules employed to transform plaintext into ciphertext and vice versa. The most secure and recommended algorithm is the Advanced Encryption Standard (AES), a symmetric algorithm capable of supporting encryption up to 256 bits. AES 256-bit encryption is the strongest encryption standard that is commercially available today.
- Encryption Keys: An encryption key is a piece of information used as input for the encryption algorithm. The key dictates how plaintext is converted into ciphertext and is also used for decryption.
- Symmetric Keys: In this method, a single private key is used for both encrypting and decrypting sensitive data. Symmetric keys offer faster performance due to the use of only one key for both operations.
- Asymmetric Keys: This approach utilizes one public key for encryption and one private key for decryption. It provides a higher level of security and eliminates the need for a secure key exchange.
Data that traverses a network or communication channel is referred to as Data in Transit. This type of sensitive data should also be encrypted. Transport Layer Security (TLS) accomplishes this by using encryption algorithms, digital certificates, hash functions, and forward secrecy.
Data stored on storage devices is known as Data at Rest. To secure this sensitive data, encryption methods like Full-Disk Encryption (FDE) and File-Level Encryption (FLE) are employed. In database security, encryption techniques include Transparent Data Encryption (TDE), Column-Level Encryption (CLE), and Application-Layered Encryption (ALE). Encrypting data at rest doesn’t necessarily encrypt data in transit, so organizations often utilize both methods to ensure comprehensive data security.
Key Management: A key management system (KMS) encompasses the management of cryptographic keys within a cryptosystem, including key generation, exchange, storage, usage, removal, and replacement. This is fundamental for protecting sensitive information, securing digital assets, and ensuring data integrity and confidentiality.
Data at Rest
Data that is stored and located at its origin should be encrypted as well. Even if stored locally, only authorized machines and individuals can view the data. There are various types of encryptions that can be used for Data at Rest each providing benefits and drawbacks.
Full-Disk Encryption (FDE)
This data security method encrypts the entire storage device or disk, making the data unreadable without the correct decryption key. One of the key benefits of Full-Disk Encryption is minimal performance impact. The initial encryption of the data can take time depending on how much data is being encrypted but once complete, the encryption/decryption is transparent to the user once they input the correct passphrase/PIN. Another benefit is effectively protecting data due to hardware theft. Without the proper decryption key, the data is unavailable.
A key disadvantage of FDE is once the decryption key is used, all the data on the disk is available. This creates a security threat if the system or decryption key is compromised. Utilizing Zero trust principles, a better approach to this encryption is providing access/decryption to the necessary files and systems as opposed to the entire system or a multi-layered security approach including FDE and granular security methods.
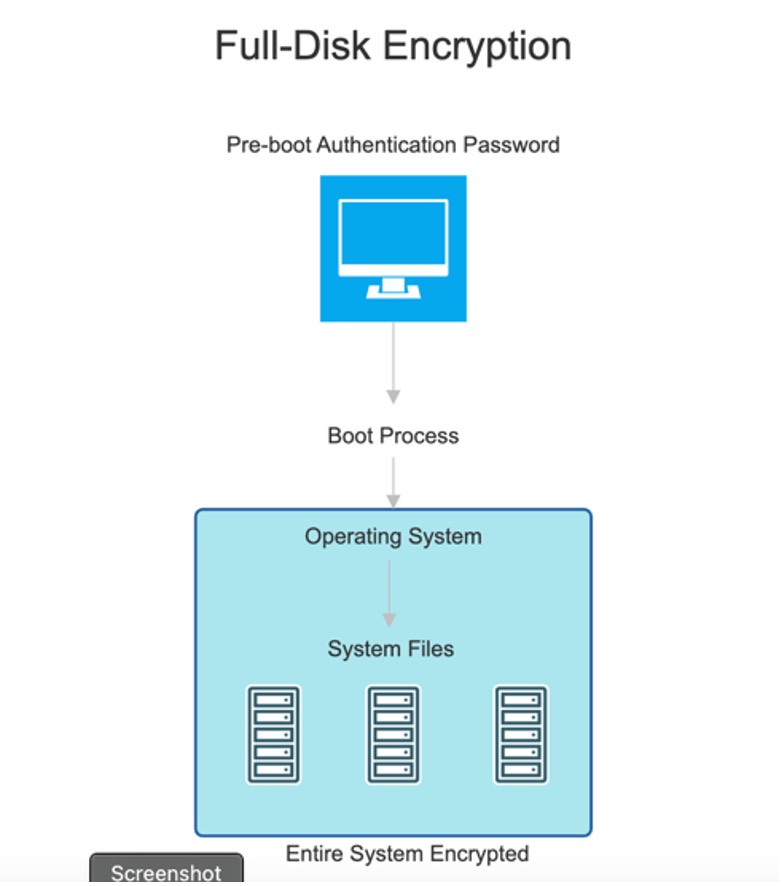
Figure 1 – FDE Process
File-Level Encryption (FLE)
This security measure encrypts individual files or folders rather than encrypting entire drives or volumes. Each file has its own unique encryption key providing additional security and complexity against a data breach. A major benefit of FLE is user granularity in encryption. Files and folders are encrypted selectively, allowing for varied access controls and security levels.
While the complexity of FLE adds an additional layer of data security, it also has its downsides. Since each file is encrypted with unique encryption key, the management of those keys can be cumbersome. A proper key management system (KMS) should be used to manage the various encryption keys. Performance can also be affected as well. With large amounts of files encrypted, performance overhead can be affected since each file has to be encrypted and decrypted individually.
Database Security
Database security is highly important and is a critical aspect of data security, which focuses on protecting the data stored within a database system and often includes sensitive and valuable information. Encryption of databases is an essential part of the security framework for an organization. There are various encryptions for databases that can be utilized dependent upon an organization needs each also with advantages and disadvantages.
Transparent Data Encryption (TDE)
This encryption is like FDE and FLE in that it encrypts the entire database, including backups, without affecting the application code or it can encrypt specific files for granularity. It has minimal impact on performance since the encryption/decryption process is handled by the database engine and is relatively simple to implement. However, a key disadvantage is the database data is only secure at rest; once it becomes data in transit, the data is decrypted, and a new solution must be utilized for encrypting data at transit.
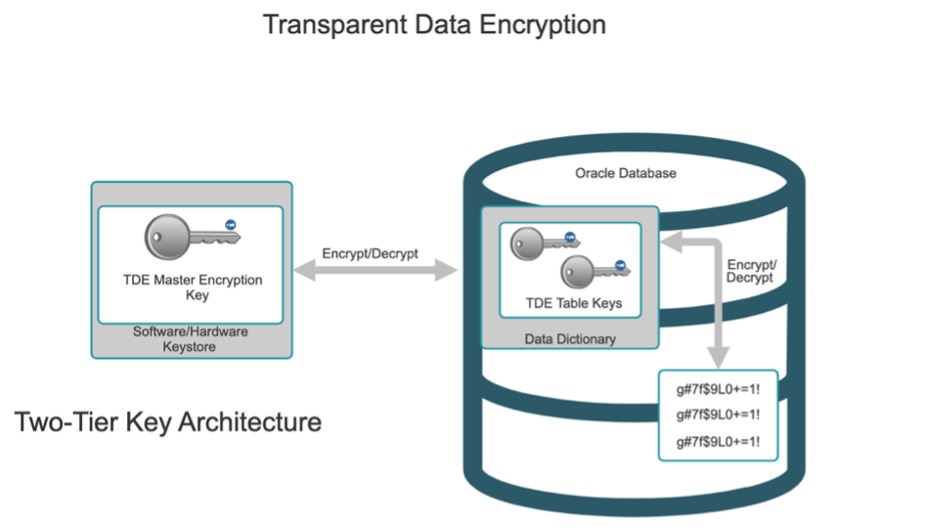
Figure 2 – TDE Process
Column-Level Encryption (CLE)
This security technique involves encrypting specific columns or fields within a database, rather than encrypting the entire database. This gives an organization a level of granularity in their security posture, allowing various levels of security applied to different types of sensitive data. Since the organization chooses what columns to encrypt, CLE can have minimal impact on performance. As with the previous encryption methods, performance can be impacted if the database system has a high throughput of data.
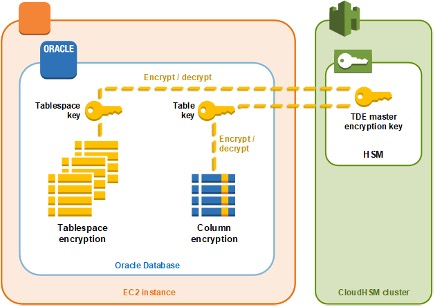
Figure 3 – CLE Example
Application Layer Encryption (ALE)
Application layer encryption is the process of imposing security encryption standards on sensitive data in the application which does not depend on the underlying layers encryption methods (transport encryption/at rest encryption). This leads to a more complex implementation including auditing the application code however a benefit of this encryption method is end-to-end security since the security of the data is not reliant on the lower layers of the OSI model. While this method of encryption is a suitable solution, the required compliance vs time and effort to achieve this type of encryption is not recommended when other suitable solutions are readily available.
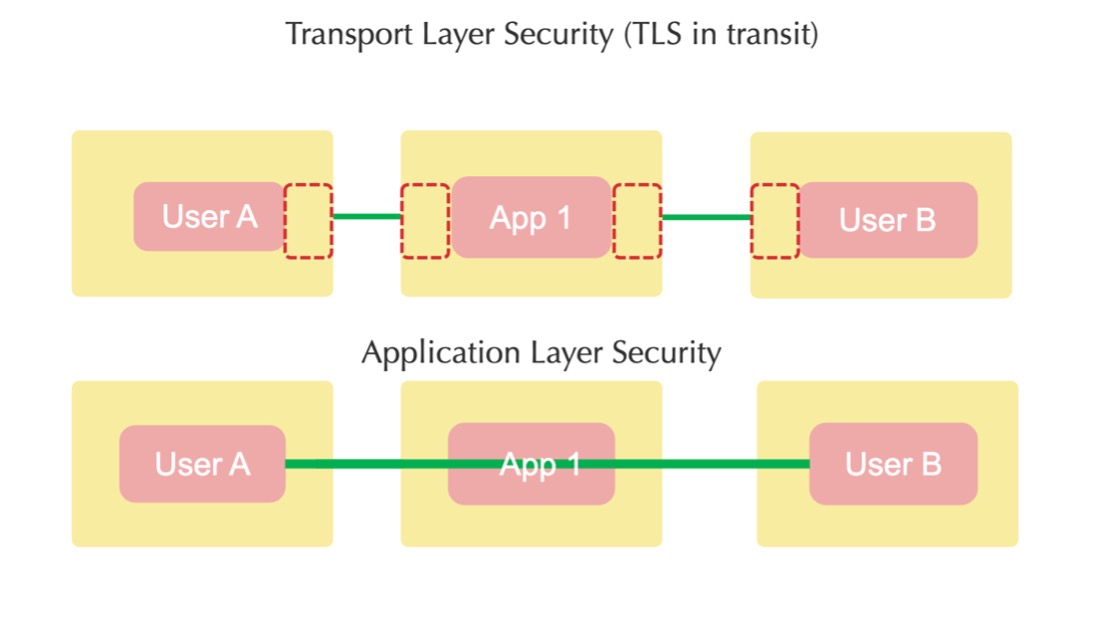
Figure 4 – TLS/ALE Example
Data In Transit
Data in transit refers to data that is actively moving from one location to another over a network or communication channel. It is important for organizations to secure their sensitive data as it travels from one location to another.
Transport Layer Security (TLS)
TLS is a cryptographic protocol that is designed to provide secure communication over a computer network and ensure confidentiality and integrity of data exchanged between two parties. The data in transit is secured by a suitable encryption algorithm, digital certificates for authentication, and data integrity using hash functions. Many benefits come along with using TLS including compatibility, consistent improvement through updated versions, and forward secrecy which prevents decrypting past communications if the private key is compromised. TLS is typically used in conjunction with HTTPS to secure web traffic. TLS does have the potential to impact performance and increase latency based on the amount of data and throughput of the data. The process of encrypting and decrypting data can impact servers and client machines if large amounts of data are traversing across the network.
Virtual Private Networks (VPN)
A VPN is a technology that allows an organization to create a secure and encrypted connection to another network over the internet. Used with IPsec, VPNS utilize strong encryption, privacy of private IP addresses, and most importantly give the ability to access private network resources over untrusted networks. Also, most VPNs are easy to implement if using a provider and relatively simple if configured directly. The downside to VPNs is the latency that can be produced due to the extra overhead for encryption and authentication.
BY STEPHON ALICEA
Senior Network Engineer