Overview
As the world of Operational Technology (OT) and the Internet of Things (IoT) expands rapidly and becomes more integrated with traditional TCP/IP networks, security has escalated from a peripheral concern to a critical necessity.
The integration of OT and IoT environments has resulted in multiple benefits, including:
- Improved efficiency
- Heightened flexibility
- Data-driven insights
However, this convergence also increases vulnerability to malicious actors. According to the 2022 Microsoft Digital Defense Report, the rise in Nation State attacks on critical infrastructure have doubled in the past year alone.
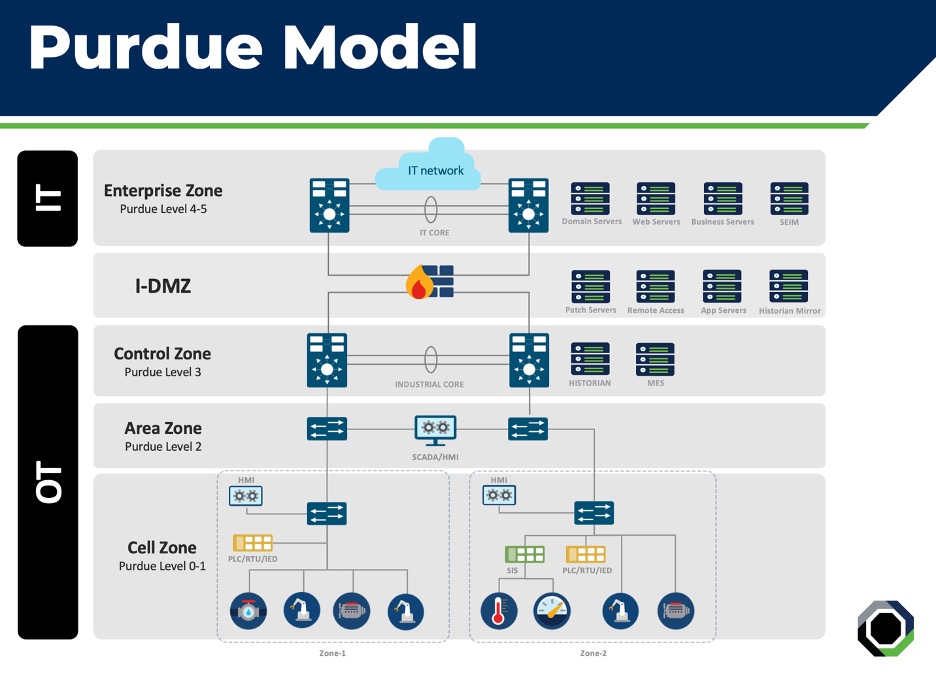
The need to secure these types of environments is urgent, yet can be incredibly challenging due to the disparity between IT and OT sectors. This post outlines a comprehensive approach to securing these environments by combining the traditional structure of the Purdue Model architecture (depicted below) with existing IT security tools and new, innovative OT monitoring tools. It also introduces a Zero Trust architecture to OT and IoT networks to establish secure, segmented networks that limit potential attack surfaces and reduce the impact of security breaches.
Goals:
CyKor’s primary goal for the development of this security strategy is to safeguard OT and IoT networks, ensuring reliability and robustness in the face of potential threats while maximizing overall security. To achieve this, the following specific objectives have been identified:
- Effective asset management is essential and includes the identification and management of all assets identified on the network. This management also extends to identifying potential security vulnerabilities identified on network assets, securing the overall security posture of the network.
- Increased visibility into OT and IoT traffic flows enables the identification of assets as they relate to the Purdue Model architecture while also monitoring for network anomalies.
- An emphasis on network segmentation by implementing detailed access control with a centralized policy management platform, reducing the network attack surface and limiting the spread of potential damage from malicious attacks.
- Improving threat detection and incident response mechanisms plays a vital role in identifying and mitigating security threats or breaches.
Challenges:
The primary challenges that are presented when working to secure OT and IoT network environments include the following:
- Legacy System and Heterogeneous Environments: The large number of end devices, many of which are constantly changing, can make it difficult to properly track and manage devices. These networks also tend to consist of legacy systems that were not designed with security in mind and often include devices and systems from a wide array of manufacturers. Together, the combination creates a complex security challenge as OT/IoT operations teams can find it difficult to properly identify devices connected to the network and ensure proper lifecycle management.
- Device Security and Patch Management: While device security and patching are a regular occurrence in traditional IT networks, these practices are often overlooked in OT/IoT networks due to the lack of vendor support for patching and the critical nature of these environments. Identifying vulnerabilities in these networks can also be a challenge due to the wide array of devices—including legacy models—across a wide array of manufacturers. This lack of regular security practices can leave networks susceptible to vulnerabilities and exploits.
- Communication Protocols and Traffic Flows: The diverse range of protocols and lack of visibility into existing traffic flows can make it difficult to ensure comprehensive network security and prompt incident response. Existing monitoring tools designed for traditional IT networks often struggle to provide proper visibility and analytics for the unique traffic patterns and protocols used in OT/IoT network environments. This lack of visibility can hinder the detection of suspicious activities, anomalies, or potential security breaches.
- Large, Flat, Unsegmented Networks: The large, flat nature of many legacy OT and IoT networks can often create a security challenge. These networks tend to allow unfettered access and communications between all devices on the network to ensure critical processes are not interrupted. However, this unrestricted access increases the potential attack surfaces, as a compromise in one part of the network can affect an entire system.
- Lack of Security Awareness and Cybersecurity Knowledge: The gap in knowledge for networking and security between traditional IT engineers and operational engineers can also be a challenge in these unique environments. While security challenges have plagued traditional IT networks for decades, OT/IoT networks have only recently begun to focus more on security. This lack of experience in these environments can increase the risk of human error, such as misconfiguration or poor security practices. An insufficient understanding of potential security threats and best practices can result in the inadvertent exposure of critical systems and processes to vulnerabilities or unauthorized access.
Solutions:
Addressing these security challenges necessitates innovative solutions that leverage cutting-edge technology, such as:
- Asset Visibility and Management: To address the challenge of asset visibility and management, organizations can implement automated asset inventory management tools that provide real-time asset visibility capabilities. These solutions can track asset properties, status, and configurations, allowing for efficient management.
- Traffic Visibility and Classification: To address this issue, organizations require specialized monitoring tools that can support the diverse ecosystem of protocols and provide in-depth visibility into OT/IoT network traffic. These tools provide analysis of traffic flows that can be used to classify devices within each zone of the Purdue model and identify traffic anomalies in real-time. Additional benefits—such as traffic behavioral patterns and deep-packet inspection—along with active and passive scanning of the network, provide organizations with enhanced capabilities such as proactive threat detection and timely resolution for anomalous activities.
- Vulnerability Management: Utilizing specialized vulnerability management solutions designed for OT/IoT environments can help identify vulnerabilities across the varied devices. This allows organizations to establish a strong vulnerability management system that can handle the diverse ecosystem of OT/IoT devices, and allows for active vulnerability assessments. Defining patch management processes are also key to maintaining a positive security posture and limiting attack surfaces.
- Access Control and Network Segmentation: Adopting a Zero Trust security model is fundamental in achieving effective access and segmentation inside OT/IoT environments. This approach enforces strict access control based on device properties, activities, and posture, thus minimizing attack surfaces. Implementing a centralized control platform that can identify assets and enforce segmentation boundaries between different segments of the network is also crucial.
- Threat Detection: To tackle the challenge of effective threat detection within OT/IoT networks, organizations should implement solutions specifically designed for these environments. This solution should incorporate behavior-based analytics, anomaly detections and machine-learning algorithms to effectively identify and respond to emerging threats effectively.
- Incident Investigation and Response: Organizations should establish a centralized incident response platform that can be used to capture and analyze security events and scrutinize incidents within the OT/IoT networks. Laying out an incident response plan that defines roles, responsibilities, and escalation procedures is also fundamental to ensuring a coordinated and efficient response. Additionally, automation and orchestration tools help with streamlining response processes, while reducing manual effort and enhancing incident handling capabilities.
Summary
Securing OT and IoT network infrastructure is crucial as these environments become more integrated with traditional networks. The convergence of OT and IoT brings numerous benefits but also increases vulnerability to malicious actors, emphasizing the need for robust security measures. Challenges in asset visibility, vulnerability management, traffic visibility, access control, threat detection, and incident response require specialized solutions.
By implementing comprehensive strategies that leverage automated asset management, specialized monitoring tools, and Zero Trust principles, organizations can enhance the security posture of their OT and IoT networks, ensuring reliable operations and mitigating risks in the face of evolving threats.
CONTACT US
For further information on architectural strategy, assessing an existing OT environment, or learning about specific security tools, please reach out to us at info@cykor.com.
CONTACT US
By Bryan Hefner
Senior Network Security Architect

